We are returning with the fourth segment of our Brilliance in the Basics series. Today’s highlight is on Endpoint Protection: a fundamental yet often neglected aspect of cybersecurity.
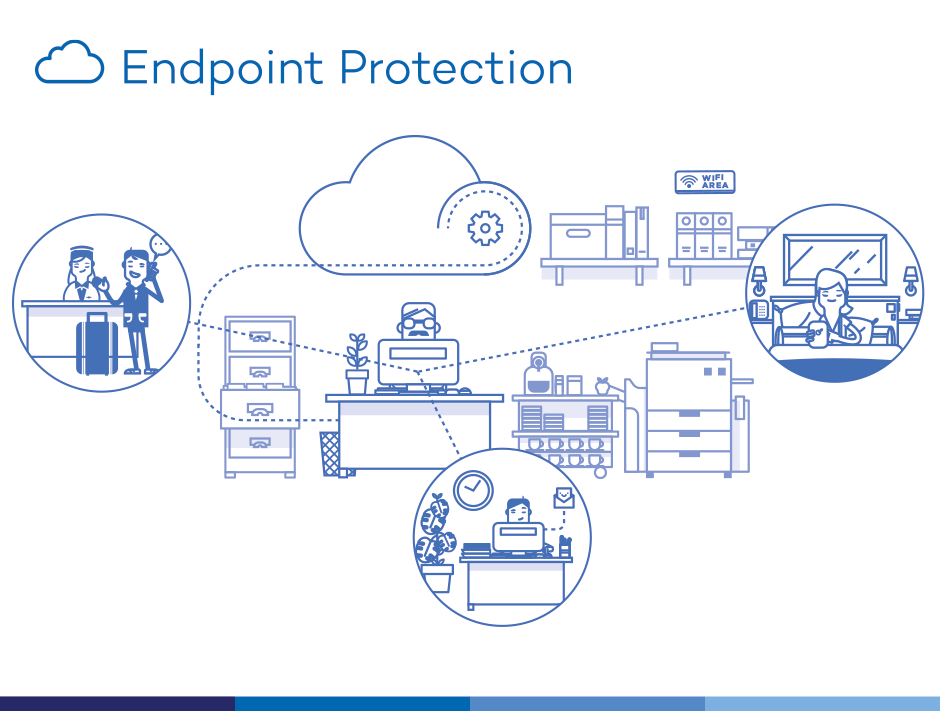
Before we dive in, let’s decode the jargon. In the world of cybersecurity, ‘endpoint’ refers to devices such as workstations, laptops, and mobile devices that connect to your network. Therefore, Endpoint Protection is about safeguarding these devices against cyber threats.
Why endpoint protection is a big deal:
1. Devices as Gateways
Your workstations, laptops, and mobile devices are gateways into your network. Endpoint protection acts like a sentinel, preventing malicious intruders from sneaking in.
2. Threats on the Move
With remote work and on-the-go access, devices are used in various environments, often connecting to unsecured networks. This mobility expands the risk landscape, making endpoint protection essential.
3. Advanced Threats Need Advanced Defenses
Cyber threats have become more sophisticated, making them harder to detect and counter. Endpoint protection platforms are designed to identify and neutralize these threats before they inflict harm.
Understanding the ‘why’ leads us to the ‘how’. Here are practical steps to enhance your endpoint security:
Actionable Insights
1. Utilize a Comprehensive Endpoint Protection Platform
Invest in a platform like Microsoft Defender, Cylance, Norton, McAfee, or Bitdefender that provides an all-around security solution, including antivirus, antispyware, firewall, and intrusion detection systems.
2. Keep All Devices Up-to-Date
Ensure your devices are equipped with the latest software, firmware, and security patches. An outdated device is akin to an unguarded fortress, inviting cyber threats.
Imparting knowledge about endpoint protection and safe device use is crucial. After all, informed users make for a robust security network.
Key Takeaways
- Devices like workstations, laptops, and mobile phones are gateways into your network, necessitating robust endpoint protection.
- The evolving nature of work and advanced cyber threats underscore the importance of endpoint protection.
- Adopting a comprehensive endpoint protection platform, regularly updating devices, and user education are crucial steps to bolster endpoint security.
That concludes Part 4, Cyber Sentinels. Remember, each device you use contributes to your overall cybersecurity. Treat it with respect, secure it diligently, and you’ll be on the right path to ward off cyber threats.
Stay tuned for Part 5, where we’ll discuss the importance of data backups and redundancy. Until then, stay #CyberSmart, and remember – securing your endpoints means securing your digital domain.